About Me
I'm a Postdoctoral researcher at CISPA Helmholtz Center for Information Security and part of the EMSEC (Embeded Systems Security Group) headed by Dr. Ali Abbasi.
My research interests are in System Security and Program Analysis leveraging Symbolic Execution, Fuzzing and Rehosting techniques.
I completed my Ph.D. in Computer Science (Cybersecurity) at SMU Singapore, where I was fortunate to be advised by Prof. Xuhua Ding.
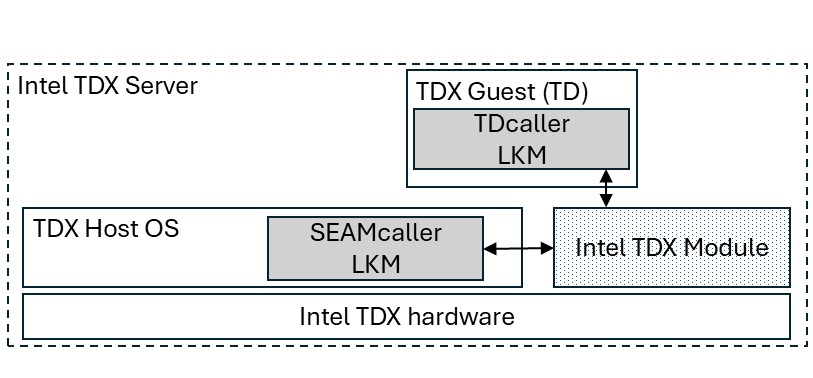
My research is driven by the goal of advancing the analysis of system programs (e.g., OS kernels such as Linux and TEE firmware such as the Intel TDX Module) and strengthening system security.
Currently, I focus on a few key challenges in this domain: (1) the difficulty of dynamically analyzing system programs that are tightly coupled with hardware and system state, (2) establishing a foothold for analyzer software to run and conduct analysis on these programs, and (3) performing program analysis with precise binary-level control and reasoning.
My work develops specialized environments using hypervisors and virtualization to host system programs, along with tools to manage their runtime state and enable analyzer software to introspect execution. By combining traditional dynamic binary analysis with symbolic execution, my work enables precise control and deep binary-level reasoning for complex analysis tasks. I enjoy tackling difficult systems-level challenges, working with C, assembly and C++, and exploring the low-level interactions between hardware and software.
Before my Ph.D. journey, I completed both my B.Sc. in Electronic and Telecommunication Engineering and my M.Sc. in Security Engineering (Computer Science) at the University of Moratuwa, Sri Lanka.
Publications

CCS 2025

CCS 2023
Projects and Tools
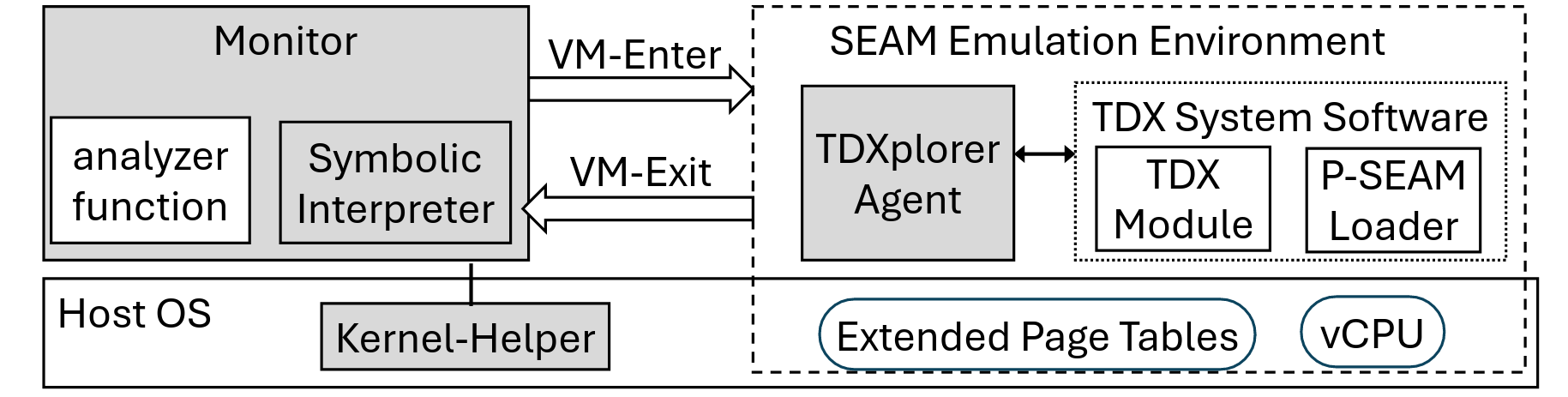
- Run the TDX Module on a desktop PC with no hardware dependency.
- Supports a wide variety of API calls: SEAM calls from the VMM and TD calls from guest VMs (TDs).
- Traditional dynamic analysis: software and hardware breakpoints (INT3, DR breakpoints), single stepping.
- Instruction and basic block tracing.
- Symbolic execution for in-depth analysis.

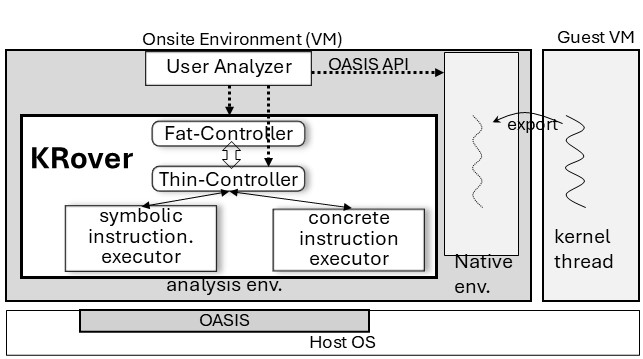
- Facilitates dynamic analysis of a single live kernel thread.
- User-programmable analysis for fine-grained binary-level control and runtime introspection of the target thread.
- Fast symbolic execution with native dispatch of non-symbolic instructions.
- Multiple analysis modes in one run: delayed symbolic start, seeded execution, and path exploration.
- Traditional dynamic analysis: software/hardware breakpoints (INT3, DR), single stepping.
- User–kernel cross-space analysis.